‘Getting Started Becoming a Cyber Warrior’ by Occupy the Web (Review)
This is a book I was itching to get my hands on as you would already know if you read my review of ‘Linux Basics for Hackers’ and I can tell you it did not disappoint.

Quite frankly the most enthralling tutorial-style book I have ever read of any kind in my 41 years in this earth, has everything I was looking for and more.
In my review, of ‘Linux Basics for Hackers’ I said:-
“If you are new to ethical hacking it can be quite scary looking at which books to get and courses to do but if anyone ever asks my advice then this will be the first one I mention, for a beginner and someone wanting a taste of Kali Linux then this book is an absolute must.”
But I am going to recommend these as a pair because where the first one focused on Linux ‘‘Getting Started Becoming a Cyber Warrior’ follows on from this and shows you tricks, tools and operations that can be used on multiple OS and the web, he covers tools from Shodan to DNSenum and Nessus to Hashcat with everything in between, it truly an awesome book that covers in-depth each subject bit not in any essay style text blocks that make you zone out.
This is the table of contents of the book and I will touch upon each I don’t want to go into too much depth as you really should go and get this book.
TABLE OF CONTENTS
- Dedication
- About the Author
- Acknowledgements
- Preface
- Chapter 1: Introduction
- Chapter 2: Essential Skills and Tools
- Chapter 3: The Hacker Process
- Chapter 4: Setting Up Our Lab
- Chapter 5: Passive Reconnaissance
- Chapter 6: Active Reconnaissance
- Chapter 7: Vulnerability Scanning
- Chapter 8: Password Cracking
- Chapter 9: Metasploit Exploitation
- Chapter 10: Sniffing and Protocol Analysis
- Chapter 11: Post-Exploitation
- Chapter 12: Web Hacking
- Chapter 13: Evading Anti-Virus (AV)
- Chapter 14: Covering Your Tracks
- Chapter 15: Wi-Fi Hacking
- Chapter 16: Malicious Python
- Chapter 17: Social Engineering
- Epilogue
- Appendix A: Cryptography Basics for Hackers
- Appendix B: Cyber Warrior Wisdom of OTW
- Index
In the opening Introduction section we speak about three things:
- Legitimate professions open to hackers.
- The history of hacking, to give you some appreciation and perspective of our discipline.
- The legal consequences of hacking, to help keep you out of the lawman’s hands.
All three are a fascinating to read and in particular, I loved the history of hacking and getting it in bite-size sections is great and in keeping with the book and Occupy The Web’s style where you get the information you need and not any excess unless it pertains to your learning.
In the ‘Essential Skills and Tools’ we cover a lot of what you will have learnt in ‘Linux Basics for Hackers’ so this is a little refresher of the tools and skills, you picked up.
‘The Hacker Process’ is a neat little chapter that speaks about fingerprinting, passive and active reconnaissance, password cracking and the mindset we should be using and thinking to go into each hack/project/CTF etc
“Hacking is a process, not a technology or tool.”
-Master OTW
NOW, we start to get going with the setting up our lab chapter and I don’t mind telling you I have been going through some amount of books and courses and this book does what the others didn’t, FINALLY a book that doesn’t JUST tell you to install Kali but also a target machines in your virtual lab including a MySQL database to hack, this is such a welcome addition.


For passive reconnaissance I will let my good friend ‘Red Team Red Shirt’ give his review on this chapter for you in one tweet:
He is a great guy so pleas feel free to check out his site at https://redteamredshirt.com/ as he is on the same journey as me from IT (he is a Web Developer) looking to jump to Ethical Hacking the same as me.
In active reconnaissance we delve deeper into Nmap which includes a cool history of Nmap but its not just this we use, we get to learn about and have a go in Hping3 as well as doing some website reconnaissance with WhatWeb, BuiltWith that is such a fun tool’s to use.

I should add that the exercises I raved so much about in my last review are back and they really are a great part of both his books and not only is he a phenomenal hacker but such a natural trainer and teacher, I will reiterate again that I wish I could afford the video training courses he does as he is that good.
Vulnerability scanning is the process of looking for known vulnerabilities and we I was ecstatic because we got to use a tool I had heard so much about and was actually aware of it being used at my work recently by the new firewall and security providers and its Nessus.

Again OTW does what he does best and explains the install process easier, giving you the step by step guide in how to set it all up and use.
We also did some more website vulnerability scanning with OWASP ZAP too which was so much fun ?
The password cracking chapter is BRILLIANT, I actually sent him a message when I finished this chapter saying thank you for the most thorough guide to password cracking I’ve seen so far in any of the training I have done and it really is that good.




In Metasploit exploitation we delve deeper into the tool including using different Metasploit Interfaces, Metasploit has multiple interfaces including;
- msfconsole – an interactive command-line like interface
- msfcli – a literal Linux command line interface
- Armitage – a GUI-based third party application (one of my favourites)
- msfweb – browser based interface
Sniffing and protocol analysis talks about several tools including TCPdump, Wireshark, Capsa and more, fascinating and along with Wi-Fi hacking is something I am desperately wanting to learn more about in the future.
In Post-Exploitation we talk about the phases of operation once a victim’s system has been compromised by the attacker, so, for instance, Do we have system admin privileges?, What payload did we place inside the system?, What service or application did we exploit?
Web hacking talks about the approaches to web hacking and tools and methods we can use like SQLmap and WPScan.

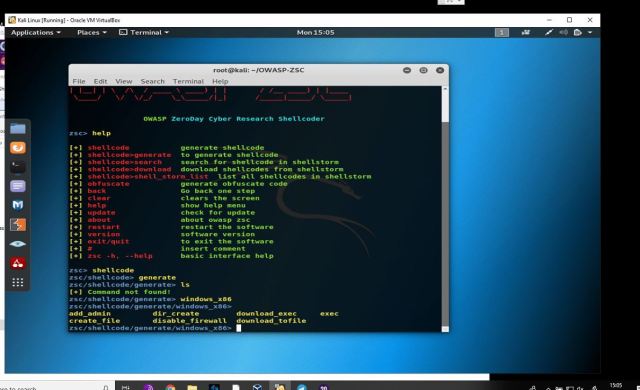
Evading anti-virus and covering your tracks are fantastic chapters as is all the rest, I actually love how going through the book is like a hack from beginning to end.
Wi-Fi hacking is brilliant, I have two Alfa USB network adaptors and a dedicated Kali machine which I got to play around with on this chapter, I am going to do an actual post just on this subject so won’t speak about it too much here other than to say this is a GREAT chapter.
Malicious python is the last chapter in the book and was another hit, it follows on PERFECTLY from ‘Linux Basics for Hackers’ and as I am trying to learn Python at the moment too I loved it.

So in summation, go buy ‘Linux Basics for Hackers’ if you haven’t already and are looking to get into ethical hacking and then purchase THIS book to go to straight after it, buy yourself a USB network adapter and have a huge amount of fun while learning a whole load about Linux, Networking, Hacking, Python and more.
Buy the book here = US = https://www.amazon.com/Getting-Started-Becoming-Master-Hacker/dp/1711729299
UK = https://www.amazon.co.uk/Getting-Started-Becoming-Master-Hacker-ebook/dp/B081Y5262X/
Occupy the Web = https://www.hackers-arise.com/
Occupy the Web Twitter = https://twitter.com/three_cube




![[DFIR TOOLS] JLECmd, what is it & how to use!](https://i0.wp.com/thesecuritynoob.com/wp-content/uploads/2023/10/2023-10-09-09_47_45-Windows-11-NO-SECURITY-VMware-Workstation.png?fit=768%2C300&ssl=1)



One Comment
Comments are closed.